Security
- You receive an email, SMS or phone call claiming to be from Hong Leong Bank or enforcement officials, asking you to provide personal financial / security information or TAC (Transaction Authorisation Code which is the six-digit number sent to a bank account owner’s mobile phone to verify a transaction).
- You receive TAC even though you did not request for it.
- You receive emails or SMS containing a URL Internet link which will lead you to a fraudulent unsecured login site.
- You receive emails requesting you to open attachments or free software that may contain malicious software like viruses, spyware and trojans that are designed to steal your personal data.
- Pop-up advertisements asking for personal or financial information are likely fraudulent, so it's better to just close them.
Using Credit card or Debit Card for Online purchases makes shopping experience more convenient but are you aware that your personal information and card data can potentially be stolen? Here are a few tips to safeguard your personal and credit or debit card information.
- Use only secured Wi-Fi connection to perform online transactions via your Internet banking website, mobile banking app or e-commerce websites. Otherwise, use your mobile data instead.
- Only perform online transactions via a secured website. Look at the URL of the website before you key in your personal and card details, if it is begins with “https” and you see a padlock in the address bar, it means the site is secured.
- Do not store your card details in a third party browser.
- Monitor your online banking transaction history and credit card statement regularly for suspicious transactions and immediately report it to your bank if there is an unauthorized transaction, even if the amount is small.
- Report lost/ stolen credit /debit card immediately. You can also report this via Connect App or Online Banking if you have registered for Connect.
- Shred any documents that contain your card details before disposing.
- Do not reveal your personal and card information such as your CARD NUMBER, CARD PIN, online banking USERNAME and PASSWORD to anyone over a phone call. If you receive a call from any Bank or Authority, please call your bank (via number stated at the back of your credit / debit card) to verify the legitimacy of the call.
- Do not send your personal and card information over any communication medium, e.g. email, SMS, WhatsApp, etc.
- Please notify the bank in advance to update your latest contact details, i.e. correspondence address, mobile number and email address.
Hong Leong Bank has incorporated the following security features:
- Up to 256-bit encryption with 128-bit minimum enabled by EV SSL certificate to secure online transactions.
- 8-16 characters of alphabets and numbers Password for all Hong Leong Connect customers.
- ATM PIN / Credit Card ATM PIN / Temporary ID for registration or reset with Hong Leong Connect. TAC will be used as an additional method to identify that it is you who is authorising the session / transaction in Hong Leong Connect Online. TAC will be auto-triggered to your registered mobile number to authenticate certain online transactions, several settings, registration and reset.
- Security Question will be prompted when an unusual online or mobile banking activity is being detected.
- Security Picture to confirm that you are accessing the genuine Hong Leong Connect Online or Mobile.
- Hong Leong Connect Online or Mobile will automatically log off if there is no activity performed after a while.
- Your Hong Leong Connect account will be considered dormant, and automatically deactivated if you do not log in for 12 months.
1. What is a TAC Scam
- TAC (Transaction Authorisation Code) is the six-digit number sent to a bank account owner’s mobile phone to verify a transaction. TAC Scams occur when the victim receives a TAC that they did not request.
- The scammers will then call the bank account owner, claiming that the TAC is actually for them and that it had been wrongly sent to the victim due to a mistake while registering their mobile phone number.
- They will ask the victim to tell them the code or forward the TAC message to them.
2. How to spot a TAC Scam call
The scammers will try to convince you that you have received a TAC belonging to them:
- “My TAC was wrongly sent to you. Can you please read or WhatsApp the TAC number?”
- “I have accidently updated your mobile number for my Internet Banking and the TAC number has been sent to your mobile phone. I desperately need to transfer money to my family member. Can you please WhatsApp me the TAC number urgently?”
3. What can you do if you receive a TAC when you did not request for it?
- Keep calm.
- Never reveal any TAC you receive to anyone under any circumstances.
- Contact the bank’s call centre and report the incident immediately.
4. Remember:
- Be sceptical. The bank will never send a TAC to you when you have not asked for it.
- The fraudster will attempt to contact you and come up with creative reasons convincing you to share the TAC. Ignore all such reasons even if they appeal to your sympathies or pressure you to do so. Never reveal TAC to anyone under any circumstances, especially if you did not ask for it.
- Call us immediately to report about the incident.
1. What is a scam call
- A Scam Call occurs when a customer receives a call from an impersonator, often from a bank and claiming a defaulted payment such as in the case of credit cards or personal loans.
- The fraudster may attempt to obtain the victim's personal banking information by claiming to be an officer from Bank Negara Malaysia (BNM) or Police DiRaja Malaysia (PDRM).
- To make it sound even more convincing, the officer may inform the victim that there is an arrest warrant under the victim’s name.
- The fraudster would then ask the victim to transfer funds into a 3rd party account.
2. How to spot a scam call
The following common phrases may help you unmask a scam call:
- "You have a credit card transaction which requires verification”, where in fact you do not have a credit card with the bank
- “You have a personal loan of RMXX,XXX which is in default”, where in fact you do not have a personal loan with the bank
- “You have an arrest warrant and you are required to transfer your money to a 3rd party account”
- “You’ve been specially selected” (for this offer)
- “You’ll get a free bonus if you buy our product”
- “You’ve won one of five valuable prizes”
- “This investment is low risk and provides a higher return than you can get anywhere else”
- “You have to make up your mind right away as there is no time to waste”
3. Modus operandi example
- Victim receives a telephone call, requesting to confirm a credit card transaction for the purchase of goods or services.
- When the victim calls the telephone number provided, the fraudsters pretend to be an agent of a bank, and again, ask the victim to confirm whether the credit card transaction had taken place.
- When the victim says that he has no such credit card or transaction, the fraudster will sound concerned and advises the victim to lodge a report with Bank Negara Malaysia's ‘Unit Kad Kredit Palsu’, or with the commercial bank's‘ credit card management department’. The victim will be given a fake telephone number to lodge a report.
- Upon calling the telephone number provided, the victim is greeted by an automated voice message identifying them as Bank Negara Malaysia. The call will then be answered by someone claiming to be a Bank Negara Malaysia officer. This person will request personal banking information under the pretense of lodging a complaint on behalf of the victim.
- The fraudster now instructs the victim to transfer money out of his/her account. The victim either withdraws cash, or transfers money, to be placed with an unknown third-party account purportedly for safe keeping or investigation.
- In other cases, fraudsters will request information relating to the victim's banking and credit card accounts. Information gained will be used to illegally transfer funds out of the victim's bank account.
4. What can you do when you come across a suspicious caller
- Keep calm.
- Do not provide any of your banking information.
- Be skeptical – Bank officers will never call you to ask for your credit/debit card or personal banking information.
- Talk to your family or friends or contact your bank call centre before taking any action.
- In doubt, please contact the bank’s call centre which can be found via the bank’s official websites or the call centre contact number at the back of your credit / debit card.
- Remember that:
- Banks never request for your personal or financial information.
- Banks never asks customers to transfer money to a 3rd party account.

What is Phishing?
Phishing is an automated form of social engineering used by fraudsters to deceive one to give away sensitive information. The initial phishing email is designed to entice the recipient to open the email and click on the links provided. The fraudsters use multiple methods to do this including enticing subject lines, forging the address of the sender, using genuine looking images or text and disguising the links within the email.
How to protect yourself from Phishing?
Never click on unknown website links or open an attachment sent via email, SMS, Twitter, WhatsApp or other popular text/instant communication applications, especially when the content is related to financial matters.


Password Cracking
Password cracking is a common way to retrieve a password by repeatedly trying to guess for the password. The most common method of password cracking is guessing and dictionary attack.

Keystroke Logging
Keystroke logging or more commonly known as key logging is a way of obtaining passwords or info by capturing what user's type. It is a diagnostic tool that comes in the form of software or hardware (i.e. inserted in the keyboard).

Login Spoofing
Login spoofing is a way of obtaining a user's username and password. The user is presented with the bank's Login page to prompt for the username and password. When the username and password are entered, the information is then passed to the attacker.

Shoulder Surfing
Shoulder surfing as it suggests, is a way of obtaining a user's username and password by peeping.

Spyware
Spyware is a computer software that is often installed into a PC without user's knowledge and usually takes place during user's download of free software, games or subscribing to free online services from the Internet. Once installed, it does not only monitor user's surfing activity but also capable of retrieving any personal and sensitive information that is being transmitted on the Internet before it is sent in the background to interested parties.

Trojan Horse
Trojan horse is a type of malware (malicious software) which allows unauthorised access by attacker to user's computer and more often for the purpose of data theft (e.g. personal information, bank account numbers and password). It can be spread through opening email attachment from unknown person or visit to unknown websites.

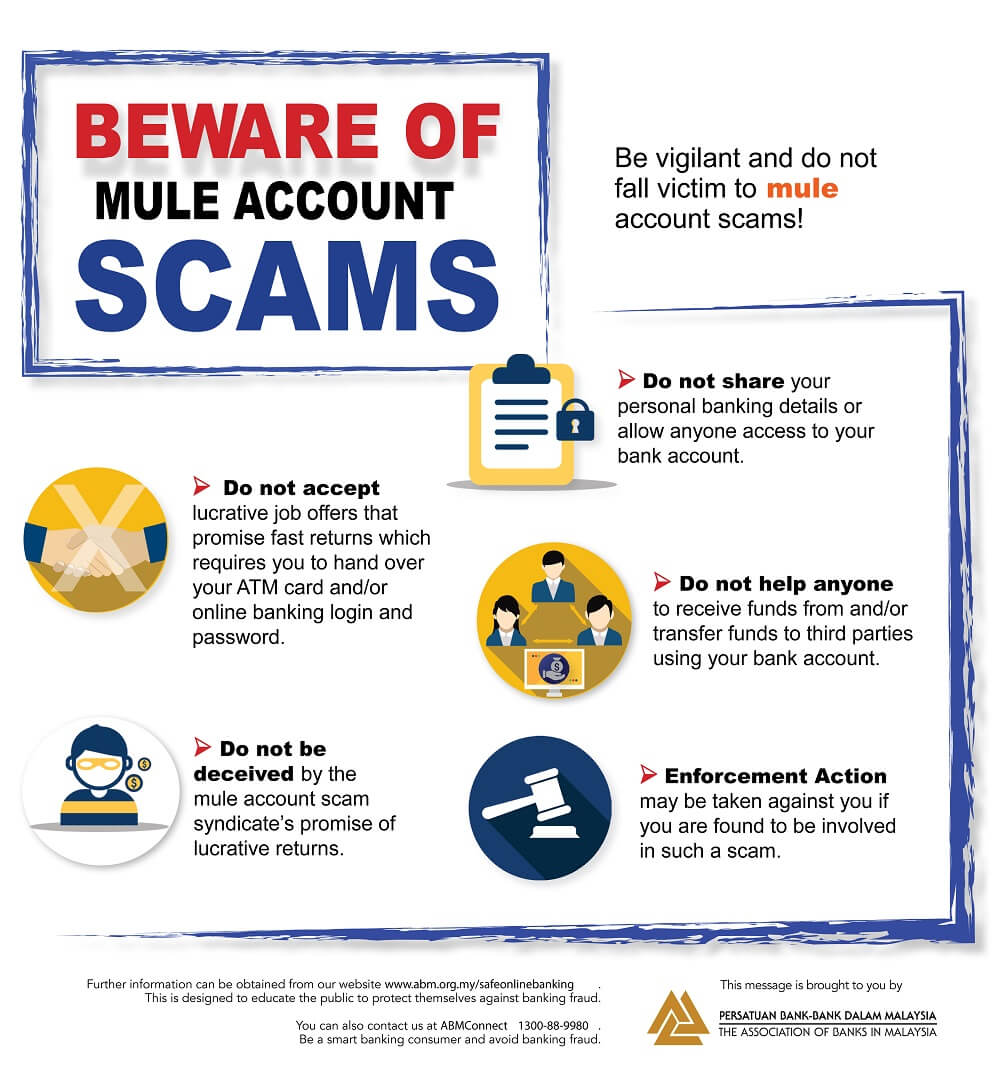
Mule Scam
As the result of responding to spam email or job recruitment that offers opportunities to make easy money, a person could fall for a mule scam. This person is known as "money transfer agent" or "money mule" whereby a mule's bank account is used to receive stolen money from phishing victims and such account also act as a transit prior to the funds being sent abroad and later to be withdrawn by the fraudsters.

ATM Card Skimming
A skimming device is used to copy an ATM card's security information on its magnetic stripe in order to reproduce the customer's information on a counterfeit card.

ATM Card Swapping
A customer's card is swapped with another card without their knowledge during an ATM transaction.

ATM Card Jamming
An ATM's card reader is tampered with the intention to trap a customer's card. The criminal removes the card once the customer has walked away from the ATM Machine.

Shoulder Surfing & ATM Pin Number Compromising
An individual stands next to someone and observes as they enter a PIN number at an ATM machine. Shoulder surfing can also be done via long distance with the aid of either a binoculars or other vision-enhancing devices.

Telephone Tapping
Telephone tapping is the unauthorized monitoring of telephone and Internet conversations and / or key tone by a third party. Phone Tapping is possible on a public switched telephone network and can be difficult to detect. To minimize the risk, consider disabling your mobile phone's Bluetooth connection to prevent any unauthorized access to signal sent from and to your phone. Visit BNM Financial Fraud Alert website for more info.
Con artist today have taken to all sorts of methods to try and trick unsuspecting victims. Their goal is to get the account holder’s private information for fraudulent uses.
We've put together a guide to show you how to do your banking safely online.

Sharing is not Always Caring
Never share information such as your username, password, MyKad number and etc. via emails or pop-up windows and phone calls.

Don't Click
Links in emails, SMS, or pop-ups. Always type the web address yourself.

Be Precise
Always type in the correct Internet banking website address directly into the address bar of your Internet browser.

Shred or Securely Store
Your printed statements.

Make It Complicated
Your password that is. Create one using a combination of alphabets and numbers, which makes it harder to guess. Make sure you never write your password down and that it's changed regularly.

Check & Monitor
View your transaction records as often as you can! This way you will notice if there is anything suspicious.

Keep It Private
Never use a public computer or an unsecured wireless network (WiFi) when performing online transactions.

Disable the Auto-Complete / Auto-Save Functions
For usernames and passwords.

Clear Your Cache
After every online session, clear your browsing cache. This function is usually found under the Internet Options section of your browser.

Look out for the Padlock Icon on Your Browser
When visiting websites that require you to share your security information, make sure the icon is there as it indicates that the websites use secure connections. For more on online safety, visit www.mycert.org.my for the latest Internet threats.

If You Doubt It, Junk It
No matter how legitimate it may seem, never respond to unsolicited emails.

Invest A Little
In computer security such as a personal firewall, anti-spy, and anti-virus software. Make sure it's updated regularly!